(Photo by Markus Winkler from Pexels)
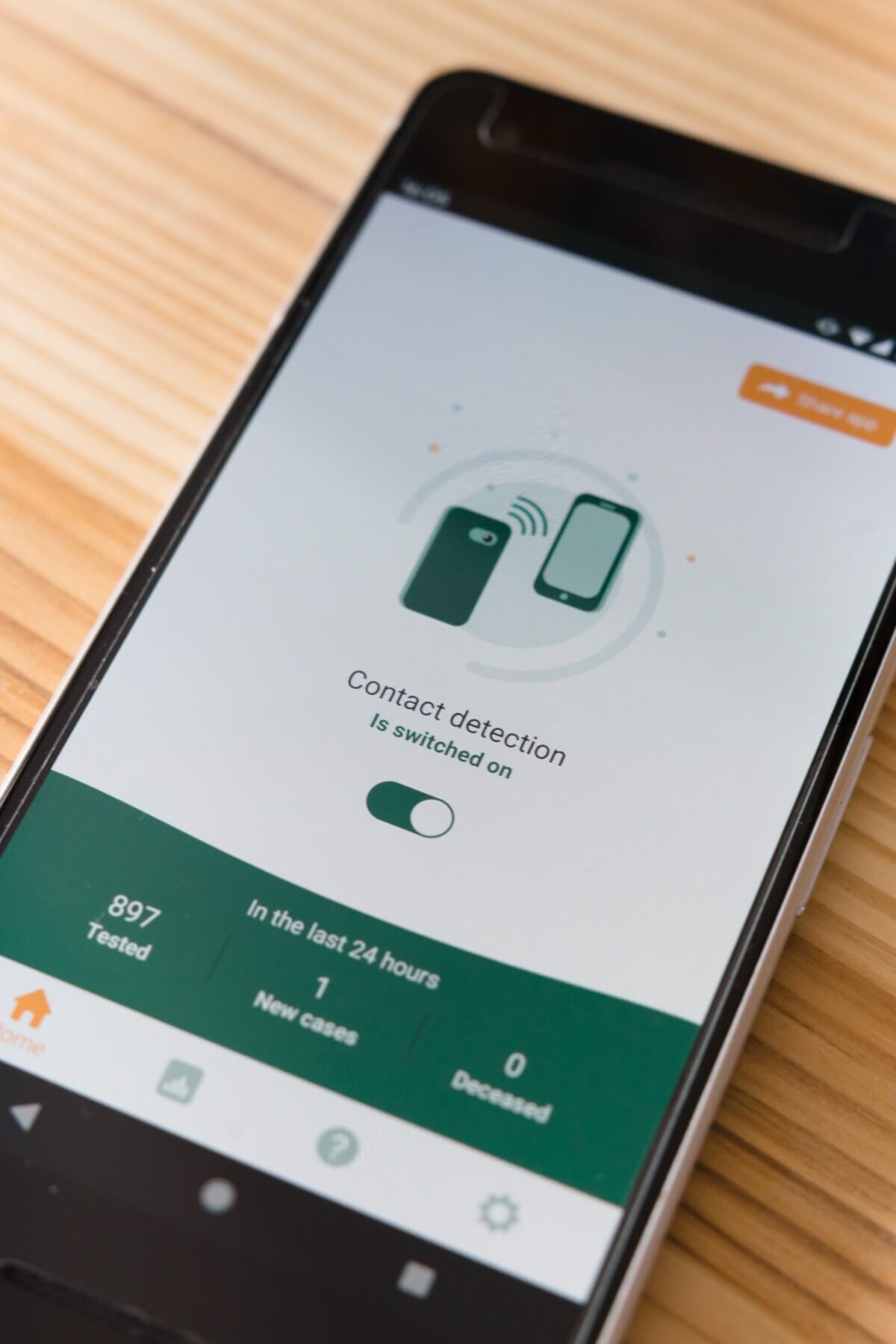
COLUMBUS, Ohio — Bluetooth devices are more susceptible to attacks that can track user location through a glitch. Researchers from Ohio State University reveal that the attackers can interact with the network and collect a user’s private data.
Bluetooth on smartphones and smartwatches helps millions communicate wirelessly — whether it’s talking, texting, shopping, or just keeping up with sports and entertainment. Yue Zhang, lead author of the study, says that this is the result of a design flaw in the technology. Zhang and his advisor, Zhiqiang Lin, were able to verify the threat by testing over 50 devices on the market and four Bluetooth Low Energy (BLE) development boards — which use less energy. They created an attack strategy called Bluetooth Address Tracking (BAT) and used a customized smartphone to hack into the devices.
Bluetooth devices have MAC addresses, which are a series of random unique numbers that identify them on a network to allow for connection between devices. Compromised MAC addresses make users vulnerable to replay attacks, which may assist attackers in monitoring the device user’s behavior, even in real-time.
“Bluetooth SIG was certainly made aware of the MAC address tracking threat, and to protect devices from being tracked by bad actors, a solution called MAC address randomization has been used since 2010,” Lin explains in a university release.
They reported the issue to the Bluetooth Special Interest Group (SIG), which oversees Bluetooth standards, hardware vendors including Texas Instruments and Nordic, and operating systems providers like Google, Apple, and Microsoft. Google was particularly grateful for this discovery, rating the findings as high severity and providing the researchers with a bug bounty award.
“This is a new finding that nobody has ever noticed before,” says Zhang. “We show that by broadcasting a MAC address to the device’s location, an attacker may not physically be able to see you, but they would know that you’re in the area.”
In 2014, Bluetooth announced a new feature called the “allowlist” that allows approved devices to be connected, while limiting private devices from accessing unknown ones. Unintentionally, this feature provides a side channel that acts as a gateway for device tracking. Luckily, Zhang and Lin have a possible solution. The team developed a prototype that counteracts this attack, called Securing Address for BLE (SABLE). This adds an unpredictable number set to the randomized address that only lets MAC addresses use them once and prevents them from being followed.
The researchers were able to stop attackers through this project. Additionally, the program has minimal downsides, only marginally reducing battery life and overall performance.
“The lesson learned from this study is that when you add new features to existing designs, you should revisit previous assumptions to check whether they still hold,” Lin concludes.
Zhang presented these findings at the ACM Conference on Computer and Communications Security (ACM CCS 2022).







